Featured Post
How Cryptographic Hash Function Works
- Get link
- X
- Other Apps
Hashing protects data from leakage compares the large chunks of data and detects the data tampering if any. 7 mod 5 2 9 mod 7 2 2 mod 3 2 10 mod 8 2.

All About Hashing Algorithms And How They Work Blockchain Cryptocurrencies Tabloid
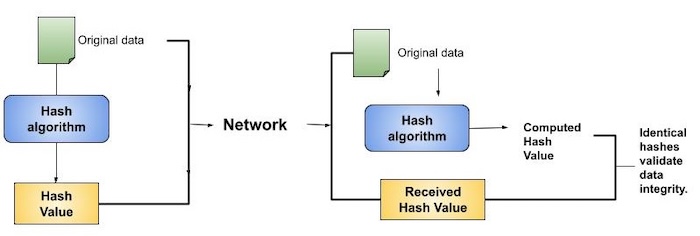
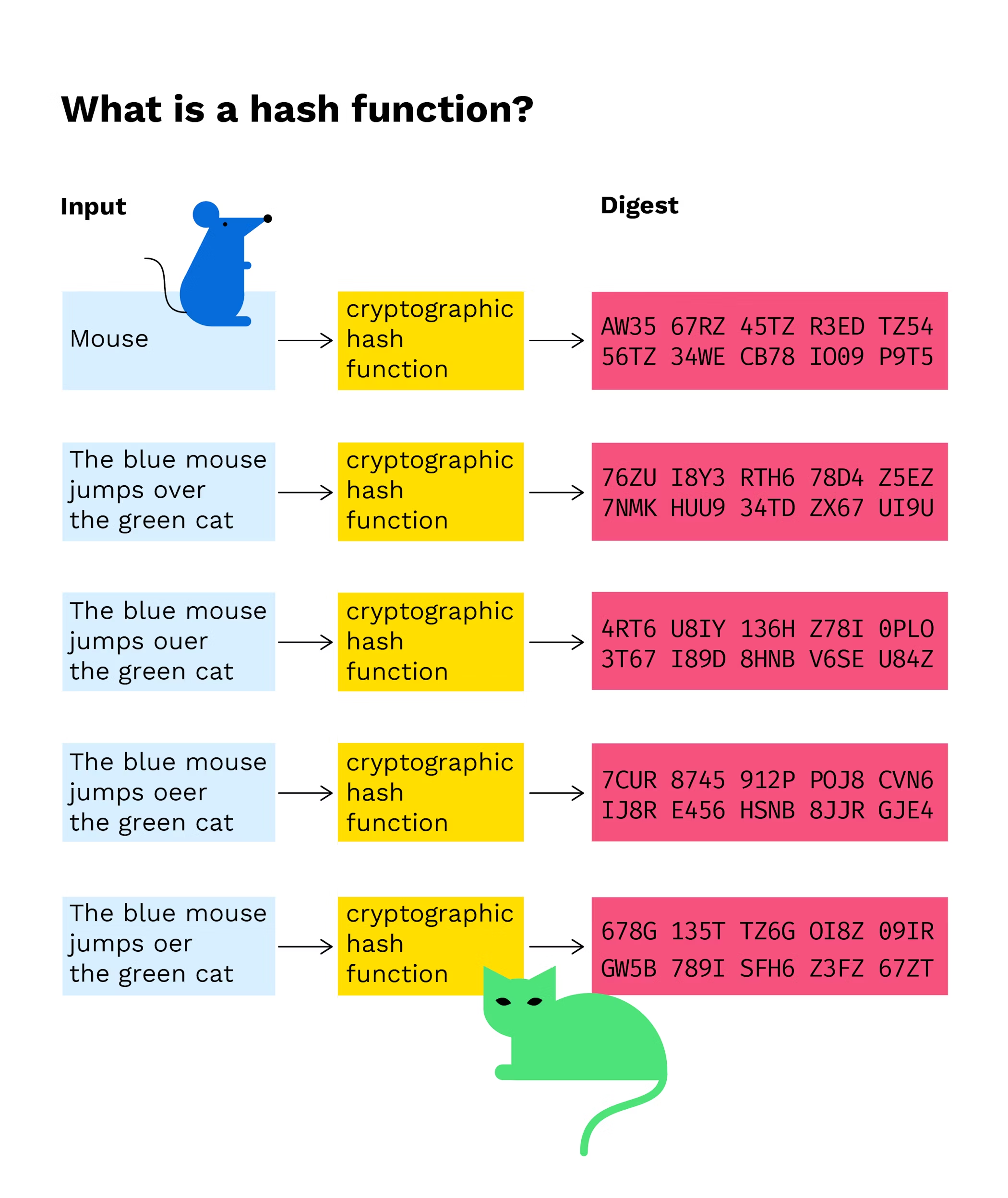
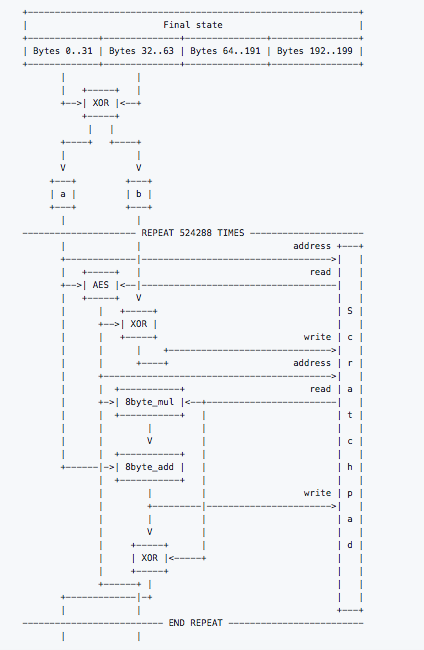
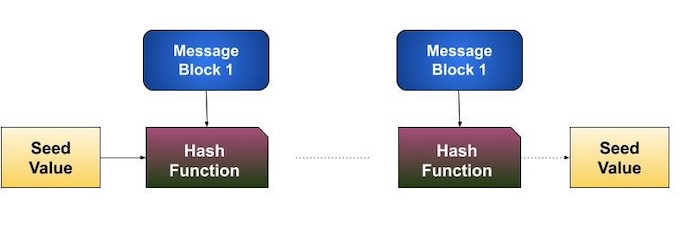
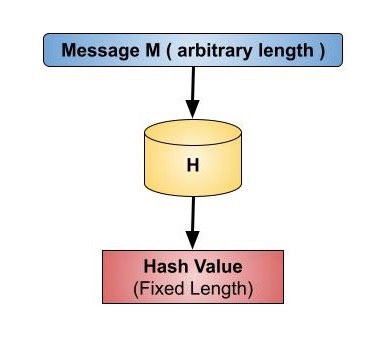
A cryptographic hash function is a one-way computational mathematical operation aka checksum or digest that takes a stream of data and returns a fix sized bit string known as cryptographic hash value this value is unique any small modification to the file will change it for example modifying a single pixel on a photograph will not be noticeable by the human eye but a.
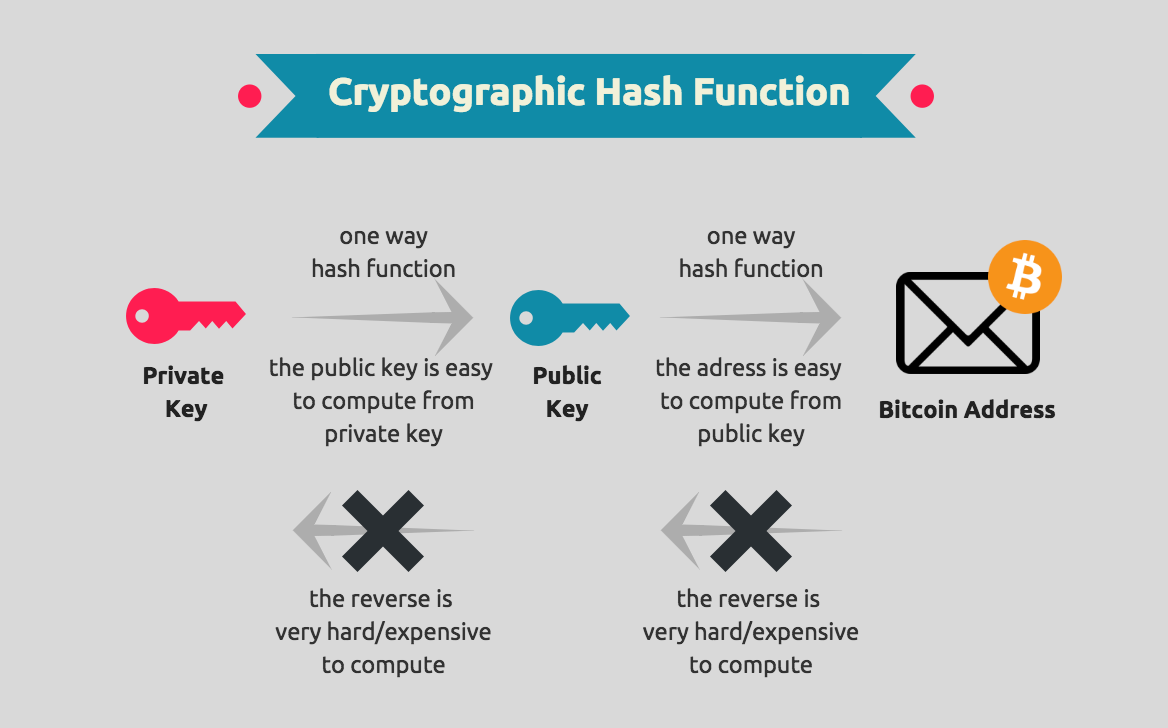
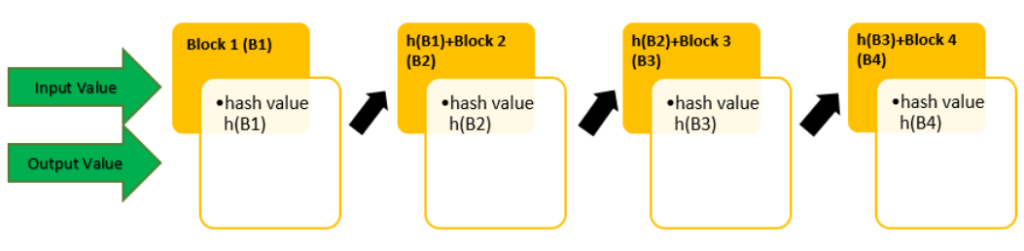
How cryptographic hash function works. In this way the formula of the Bitcoin hash power is the following. What Is a Hash Function. In the context of cryptocurrencies like bitcoin the transactions are taken as input and run through a hashing algorithm bitcoin uses SHA-256 which gives an output of a fixed length.
To accept an input of arbitrary length and output a fixed length result. A cryptographic hash function CHF is a mathematical algorithm that maps data of arbitrary size often called the message to a bit array of a fixed size the hash value hash or message digest. Three of the main purposes of a hash function are.
It is a one-way function that is a function which is practically infeasible to invert or reverse the computation. To manipulate data irreversibly. But whats its practical utility.
Applications of Cryptographic Hash Functions. In the abstract a hash function is a mathematical process that takes input data of any size performs an operation on it and returns output data of a fixed size. According to the algorithm the mining speed should remain the same 600 seconds.
Hashing is the process of sending data through a hash function to produce a specific essentially unique hash of a fixed length. Finding a previously unseen message that matches a given hash values. The input cannot be derived from the output.
A pre-image is what we call a value that produces a certain specific hash when used as input to a hash function the plaintext value. A hash function in cryptography is used to map data integrity. Hashpower blocks found in 24 hoursexpected number of blocks x work600.
The higher the Bitcoin hash rate the more difficult the mining parameter. This way the attacker cannot guess or find the password even if the database of hashes is compromised. To scramble data deterministically.
A cryptographic hash function is considered insecure from a cryptographic point of view if either of the following is computationally feasible. Finding collisions in which two different messages have the same hash value. In simple terms hashing means taking an input string of any length and giving out an output of a fixed length.
When you log in using your password the function runs through your password input and matches the hash output with the previously stored hash. All the above things about the cryptographic hash function are theoretical. When using a cryptographic hash function we must not be able to find a pre-image by looking at a hash.
In blockchain applications we use cryptographic hash functions such as SHA-256.
What Is A Hash Function In A Blockchain Transaction Bitpanda Academy

Bitcoin Cryptographic Hash Functions Video Khan Academy
What Are The Cryptographic Hash Functions And For What Purposes

Cryptographic Hash Function In Java Geeksforgeeks

All About Hashing Algorithms And How They Work Blockchain Cryptocurrencies Tabloid
Hash Function In Cryptography How Does It Work Infosec Insights
The In S And Out S Of Cryptographic Hash Functions Blockgeeks

Bitcoin Cryptographic Hash Functions Video Khan Academy

The Definitive Guide To Cryptographic Hash Functions Part 1

Hash Function In Cryptography How Does It Work Infosec Insights

How Cryptographic Hash Functions Solve A Very Difficult And Important Problem By Bennett Garner Medium
The In S And Out S Of Cryptographic Hash Functions Blockgeeks

Cryptographic Hash Functions Definition Examples Study Com

Hash Function In Cryptography How Does It Work Infosec Insights
Cryptographic Hash Function Download Scientific Diagram

Hash Function In Cryptography How Does It Work Infosec Insights
Comments
Post a Comment